From Target Detection to Strike with Zero Delay: AI Leads the US–Iran Confrontation [Lee Jong-yoon’s Military World]
- Input
- 2026-03-15 18:33:41
- Updated
- 2026-03-15 18:33:41
[Financial News] The current Middle East war and the US–Israeli military operations against Iran have revealed a radical transformation: the full-scale emergence of intelligent artificial intelligence (AI) kill chain networks. According to recent announcements by United States Central Command (USCENTCOM) and the Israel Defense Forces (IDF), the coalition conducted precision strikes on about 1,000 key Iranian military facilities per day in the early phase of the conflict. As of the 11th, US–Israeli forces had neutralized more than 5,500 targets inside Iran. The Islamic Revolutionary Guard Corps (IRGC) has also claimed through local media that over 9,000 targets across Iran were attacked during the first 10 days of the war.
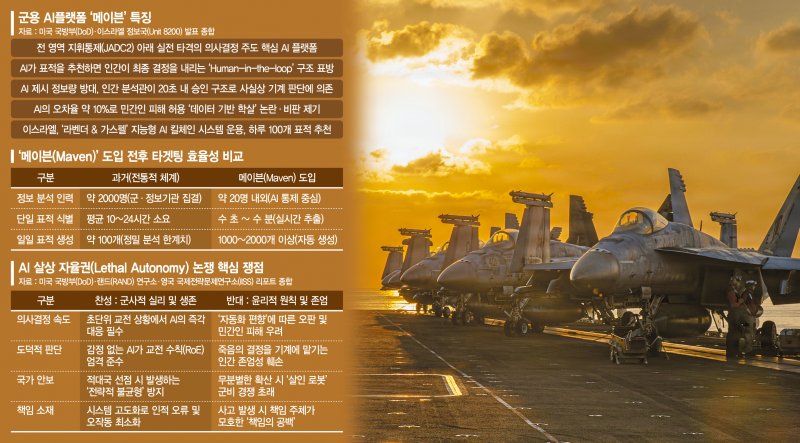
National Defense University (NDU) previously assessed that, in the early stages of the Russo-Ukrainian War in 2022, it took on average 30 minutes to one hour to go from detecting a single target to striking it. In the current conflict, that time lag has been reduced to nearly zero. From a military history perspective, this marks a revolutionary shift in command-and-control systems and a fundamental change in paradigm. A new era of “hyper-connected and hyper-intelligent” warfare, driven by data and algorithms refined through the Russo-Ukrainian War, has now fully arrived.■ Palantir identifies the target, Claude takes aimBehind this innovation lies the United States Department of Defense (DoD)’s integrated AI, the Maven Smart System (Project Maven). The system combines Palantir Technologies’ Artificial Intelligence Platform (AIP), a big-data analytics platform, with Anthropic PBC’s generative AI, Claude. Within a single architecture, these two AI engines cross-check each other to reduce errors and derive optimal solutions on the battlefield.
Within the Maven system, AIP first activates a hyper-connected surveillance network that can collect even faint biometric signals leaking from a target’s smartwatch. It is reported to have reached the stage where it can analyze trillions of data fragments gathered worldwide and structure them into data on hidden enemy movement patterns and psychological states. Claude then takes the baton within the same system, calculating the probability of mission success in detail and designing strike scenarios. It not only computes the optimal angle of approach for bunker-buster missiles, but also recommends the best combination of weapons to minimize collateral damage. In this process, the US military pits the two AI models against each other, effectively launching an “algorithmic war” that determines tactical success or failure. Acting as a staff officer that surpasses the cognitive limits of human commanders, AI has dramatically accelerated the tempo of the battlefield.■ An era when even an HDMI cable becomes an antennaThe prerequisite for this level of intelligence is a massive neural network spanning the battlefield. Under the United States Department of Defense (DoD)’s Joint All-Domain Command and Control (JADC2) concept, the US has, for the first time in combat, deployed fire-control military satellites that issue guidance commands to interceptor missiles. On top of that, every sensor is linked into a hyper-connected grid: uncrewed drones at various altitudes, human intelligence (HUMINT) assets on the ground, and even hacked closed-circuit television (CCTV) systems. These sensors form the “eyes” of the battlefield—its detection, surveillance, and reconnaissance layer. The “shooters,” the “fists” of the battlefield, are likewise dispersed across all domains—land, sea, air, space, undersea, and beyond the horizon—through a wide array of weapons systems.
The defining feature of this new battlespace is that sensors and shooters are no longer bound to a single weapons platform. Instead, they have been fused into independent, interoperable networks. For the enemy, this means that even if they are detected by forces in front of them, the missile, shell, or bullet that actually strikes could come from the rear, from above, or from any direction in a full 360-degree sphere—an experience of extreme psychological pressure. The traditional, platform-centric and linear logic of warfare has been completely shattered.
In a recent report, RAND Corporation concluded that “the outcome of future wars will depend on the robustness of intelligent networks that process vast amounts of battlefield data.”
Yet a fully connected battlefield carries a paradoxical risk: if even a single node is compromised, the entire system can collapse. There are now techniques that exploit tiny voltage fluctuations in a High-Definition Multimedia Interface (HDMI) cable linking a computer and monitor, using it as an antenna to exfiltrate information. In other words, the metal chassis itself can become a giant antenna transmitting sensitive data.
The US military’s response to this threat is, somewhat unexpectedly, quite traditional. Even as it runs cutting-edge AI platforms, it maintains a hybrid security architecture in which the final operational phase relies on analog “paper envelope codes” that cannot be hacked. This “analog fastidiousness,” aimed at eliminating any possibility of digital leakage at the source, serves as the last line of defense in a hyper-connected battlespace. For the South Korean military, which faces persistent cyber threats from the Democratic People’s Republic of Korea (North Korea), building such multilayered security networks is no longer optional but a matter of survival.■ A ‘quantitative offset’ strategy that goes beyond qualitative superiorityIn a hyper-connected battlespace, simply possessing superior weapons systems does not guarantee military dominance. Simulations by the Air Force Research Laboratory (AFRL) show that swarms of low-cost uncrewed aircraft, once they exceed a certain threshold in numbers, can neutralize the qualitative advantages of high-performance crewed platforms. This suggests that Lanchester’s Second Law, a foundation of modern tactics, still applies in the digital battlespace: the total combat power is proportional not to the performance of individual weapons, but to the square of their numbers.
The United States Department of Defense’s Replicator Initiative, aimed at rapidly expanding uncrewed capabilities, is a direct product of this strategic assessment. Even the world’s strongest military power now proclaims that “an era in which cheap, smart weapons saturate the battlefield” has arrived, and is shifting its strategic posture accordingly. Responding to North Korea’s massed, outdated arsenals solely with expensive precision munitions would be a path to self-defeat in a war of attrition. The South Korean military likewise needs to secure a “quantitative offset” capability by deploying large numbers of low-cost, high-intelligence swarm weapons—similar to the US military’s Low-cost Uncrewed Combat Attack System (LUCAS)—to overwhelm enemy mass with its own mass. Complacency in qualitative superiority can become a fatal poison. It is now time, analysts argue, for the nation to focus its resources on fielding tens of thousands of intelligent “eyes” and building multi-layered deterrent power.■ The proven power of the US JADC2 systemThe “hyper-connected and hyper-intelligent” battlespace demonstrated in the Middle East war clearly shows that the US military’s Joint All-Domain Command and Control (JADC2) architecture has entered a mature phase as a massive, cloud-based integrated system. Leading military think tanks such as The International Institute for Strategic Studies (IISS) have recently reported that “the outcome of future wars will depend not on sheer destructive power, but on organic connectivity.”
On the Korean Peninsula, a potential flashpoint where liberal democracies and authoritarian regimes confront each other, securing “technical interoperability” that allows immediate access to the US military’s hyper-connected networks has become a decisive factor that could determine victory or defeat in a contingency. Security debates must therefore move beyond the old framework of physical command authority and shift toward a new paradigm centered on securing practical “data sovereignty.”
In an age of hyper-connectivity where the boundaries of the battlefield have effectively disappeared, the true strength of the ROK-US Alliance for the Republic of Korea (South Korea) lies not in troop numbers, but in the advancement of systemic interoperability and “substantive deterrent power.” At this turning point—where the flow of data, more than the chain of command, determines national survival—military experts broadly agree that South Korea’s armed forces must look beyond formal authority and focus on securing a real stake in the allied network itself.
wangjylee@fnnews.com Reporter Lee Jong-yoon
wangjylee@fnnews.com Lee Jong-yoon Reporter